Configuring Firewall in ISPmanager5
Firewall Configuration Guide in the ISPmanager Control Panel
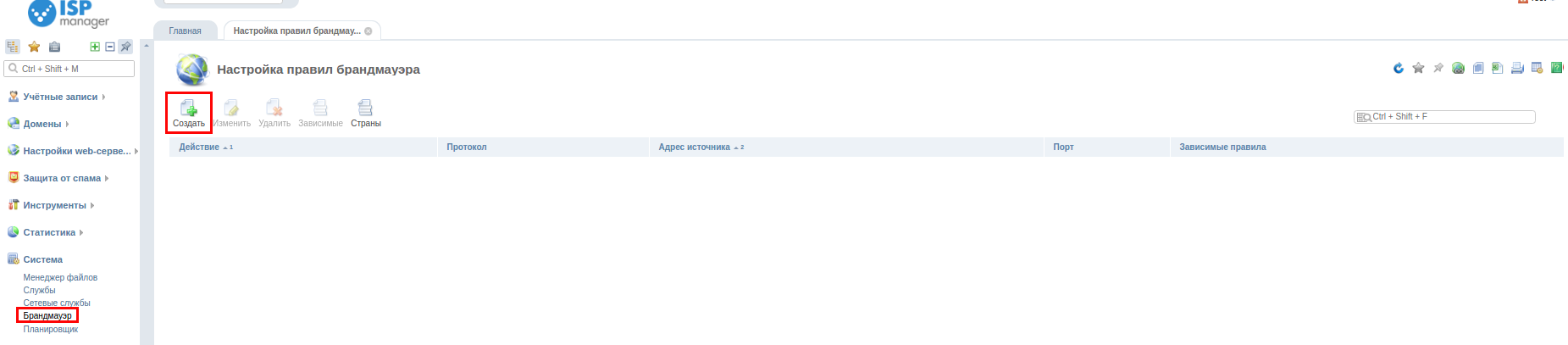
To create a new rule in ISPmanager, go to "System → Firewall" and click "Create"
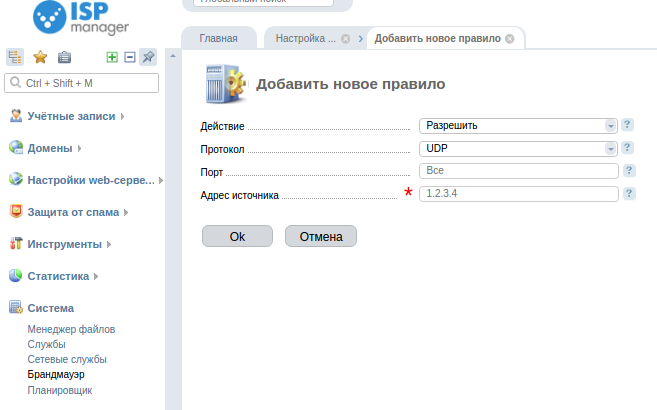
After you click on the button, a window will appear with the rule setting.
-
Action - action on the package, according to the set rule:
- Allow - filtering is disabled, server accepts connections from any IP address.
- Partially allow - server accepts connections only from specified IP addresses.
- Deny - the server does not accept connections from any IP address.
- Partial Deny - the server accepts connections only from those IP addresses that are not on the block list.
-
Protocol - data transfer protocol.
-
Source address - sender IP address.
-
Port - destination port.
Dependent rules - number of dependent rules. Dependent rules are:
-
for "partially banned" networks - firewall rules for ip-addresses from this network with the "deny" action.
-
for "partially allowed" networks - firewall rules for ip-addresses from the given network with the action "allow".
Adding firewall rules
Ubuntu/Debian/CentOS the first time you start ISPmanager, the following chains will be created in iptables:
-
ispmgr_deny_ip - contains banned ip-addresses
-
ispmgr_allow_ip - contains allowed ip-addresses
-
ispmgr_allow_sub - contains allowed subnets
-
ispmgr_deny_sub - contains allowed subnets
These chains are added to the end of the INPUT table in the order of their description. In CentOS, enabling rules necessary for correct operation of the control panel and some services (FTP, WEB, EMAIL) are written to the INPUT table before these chains are created. Each chain is assigned a pool of 10,000 entries. That is, the number of rules specified in each of the chains should not exceed 10000, otherwise it can lead to errors.
-
Parameters added to these chains independently may be incorrectly recognized and edited from ISPmanager.
-
Please remember that rules described in the ISPmanager firewall will be used to filter the network traffic only after the custom rules that were described before you installed ISPmanager.
-
Please note that if you manually configure the firewall (bypassing ISPmanager), the Firewall module "Firewall" may result in an undefined behavior of the target operating system firewall.
When adding/removing each rule using the firewall, the control panel checks whether this action will make the server unavailable from the IP address, from which it connects to the control panel. It also checks that the server IP addresses remain available for requests from within the server itself. Rules related to subnets or specific IP addresses of another rule's network are logically grouped by the control panel and displayed as nested rules.
Additional parameters
All parameters are added to mgr5/etc/ispmgr.conf file.
Option FirewallCheckAccess - this parameter allows you to add prohibiting firewall rules regardless of the restrictions of the module itself.
Paths for rules file
Ubuntu/Debian
/etc/ispipable.conf
Script loading **/etc/network/if-up.d/ispmgrfw
CentOS
Standard /etc/sysconfig/iptables
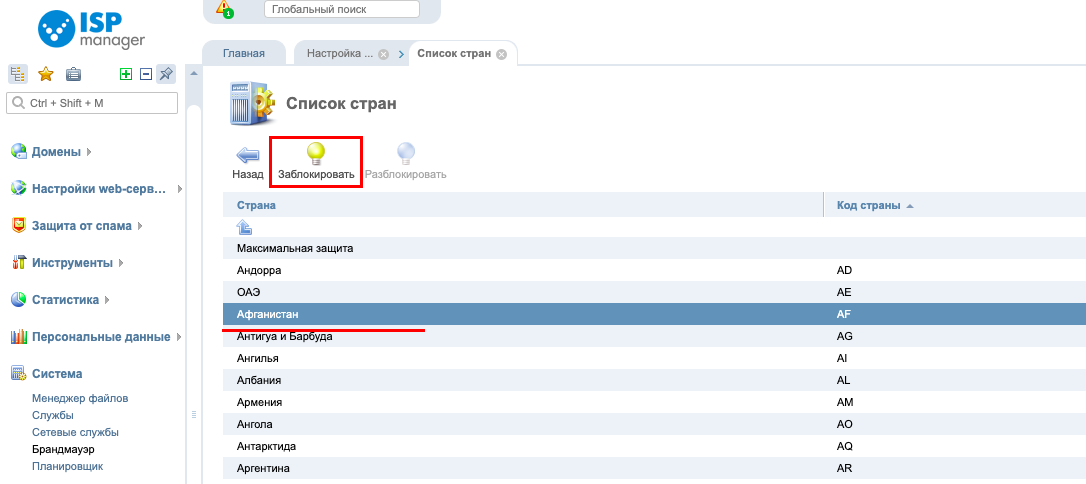
Blocking by geo
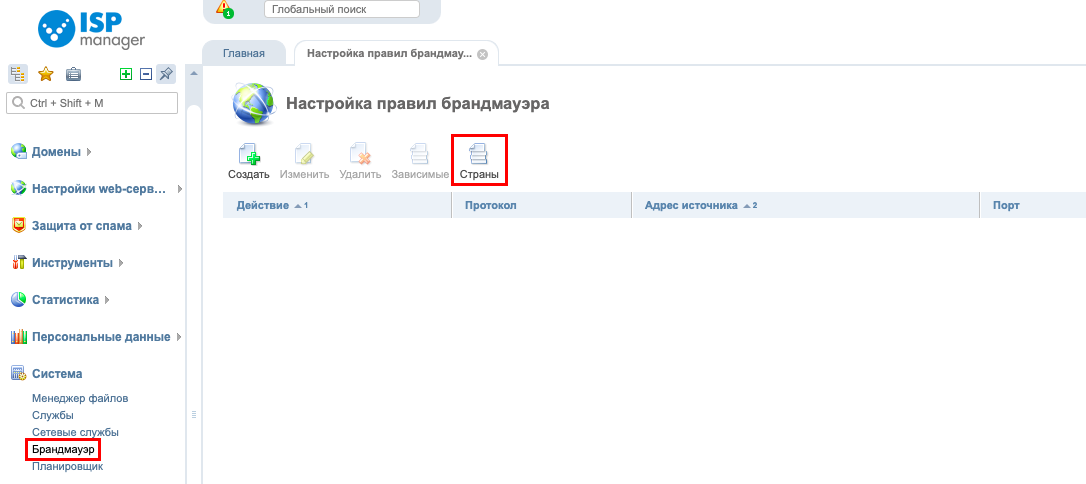
In this section you can also restrict access for users from certain countries.
To do this, click "Countries"
Select the desired country and click Block